SOC 2 Implementation Overview
We have a well-defined 6-phase Methodology, to help an organisation achieve successful SOC 2 compliance.
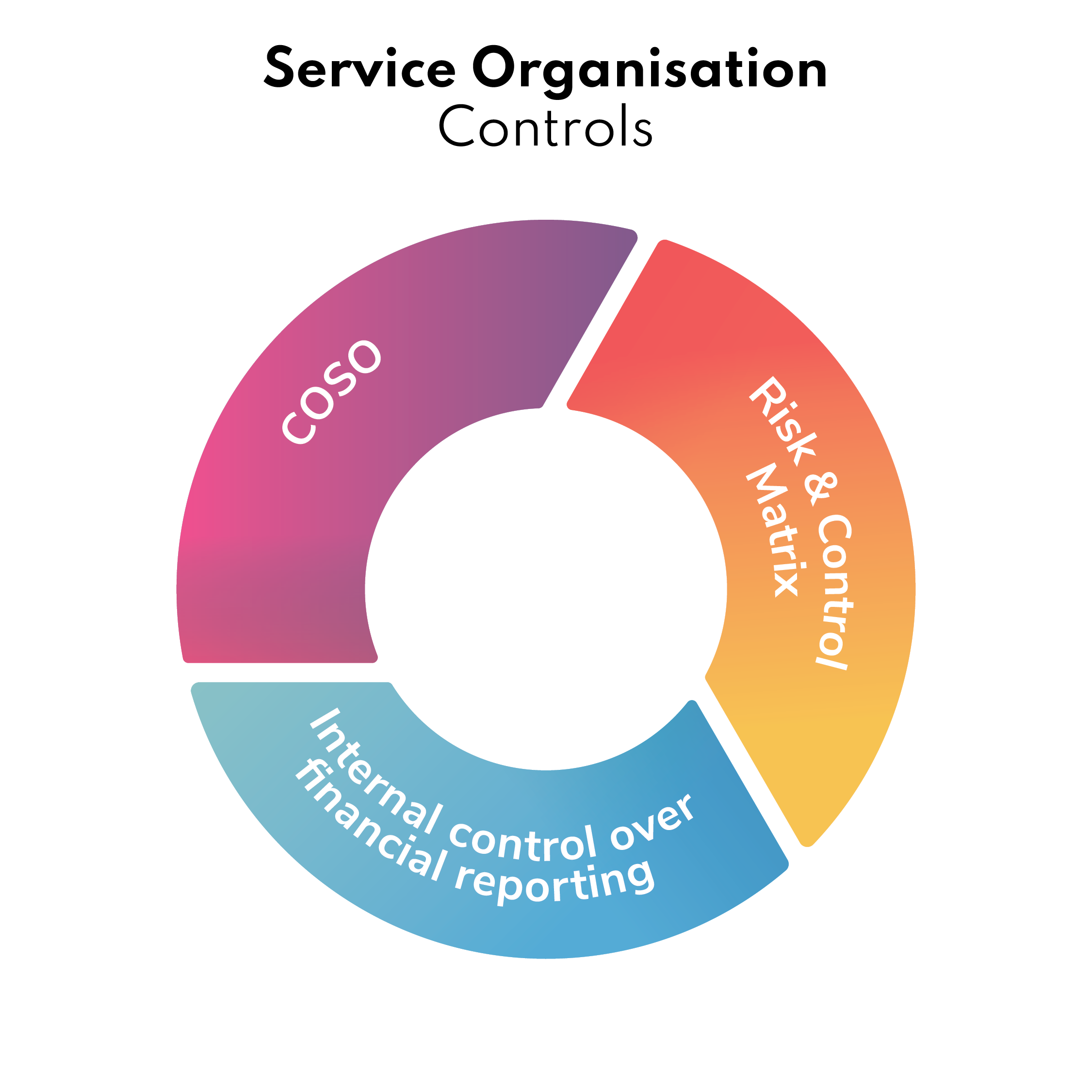
What are the SOC 2 Trust Principles
Project Phases
PHASE IDetermination of Objectives
This phase involves determining key business objectives, from user entity, as well as of the service organisation.
PHASE IIGap Analysis
This phase involves performing gap analysis of the above listed objectives on one hand, and the applicable SOC 1 controls and risks, on the other. We provide solution for all identified gaps.
PHASE III Control Design and documentation
This phase involves our methodology that involves distribution of risks, and control responsibility to internal stakeholders. This also includes nomination of key roles such as risk officer – who will drive the ongoing compliance.
PHASE IVTracking
This phase involves tracking the client risks, documentation and self-compliance on a weekly basis till all internal controls are adequately implemented.
PHASE V Performance Tracking
This phase involves showcasing client with changes in a given period by providing change specific score of compliance between 0 -100%. This gives the organisation an evidence of a measurable framework of demonstrating internal controls.
PHASE VIInternal Audit
Internal audit followed by a formal review of the program gives organisation an independent perspective, and enables them to be ready for final attestation.
At this stage the client has implemented the governance system in completeness. Generally upon completion of one month of this, the organisation can achieve SOC 2 – Type 1 attestation, and upon completion of 6 months, the client can achieve Type 2 attestation. Here the assumption that all risks are under control that will give adequate assurance to the user entity.
Training
We provide bespoke training, listed below are our offerings.
- Shorter Sessions from 1 hour to 4 hours
- Interpretation of the ISO 27001 requirements
- 1 Day Awareness Session
- 2 Days Internal Audit Course
- 3 Days Implementation Course covering 10+ hands on exercises
Upon receiving your request, we will provide you further details.
Documentation Toolkit
ISSO 27001 requires documentation of policies, procedures and records. As a result of several consulting assignments, we have some of the best content available that covers all the requirements. Our documentation has the following salient features:
- Alignment with all ISO 27001-documentation requirements
- Our experiences turned into documentation templates
- Project Tracking tools to support the implementation
- Q & A support
Upon receiving your request, we will provide you further details.
Internal Audit
An independent assessment helps to assess the state of compliance. Our internal audit methodology includes people, process, technology and measurements to assure and provide management the degree of ISO 27001 compliance. Typically 3-5 days is required to perform a comprehensive internal audit. Upon receiving your request, we will provide you further details.
Annual Risk Assessment
Risk Assessment is a mandatory requirement for achieving and maintaining ISO 27001. We have one of the most comprehensive risk assessments that comprises asset, controls and security policy objective wise risk assessment. Let us know if you are interested. Upon receiving your request, we will provide you further details.
Program Management
Our consulting methodology experience has helped us to understand – what it takes to design and maintain a successful ISO 27001 compliance. ISO 27001 Program management removes the compliance responsibility to an external team, whereas the management focuses on customer/business delivery. We currently manage program management for customers who has one location to another set of customers who have more than 8 locations worldwide Upon receiving your request, we will provide you further details.